Risk Assessment in the County of San Mateo, California
| Risk Assessment in the County of San Mateo, California | |
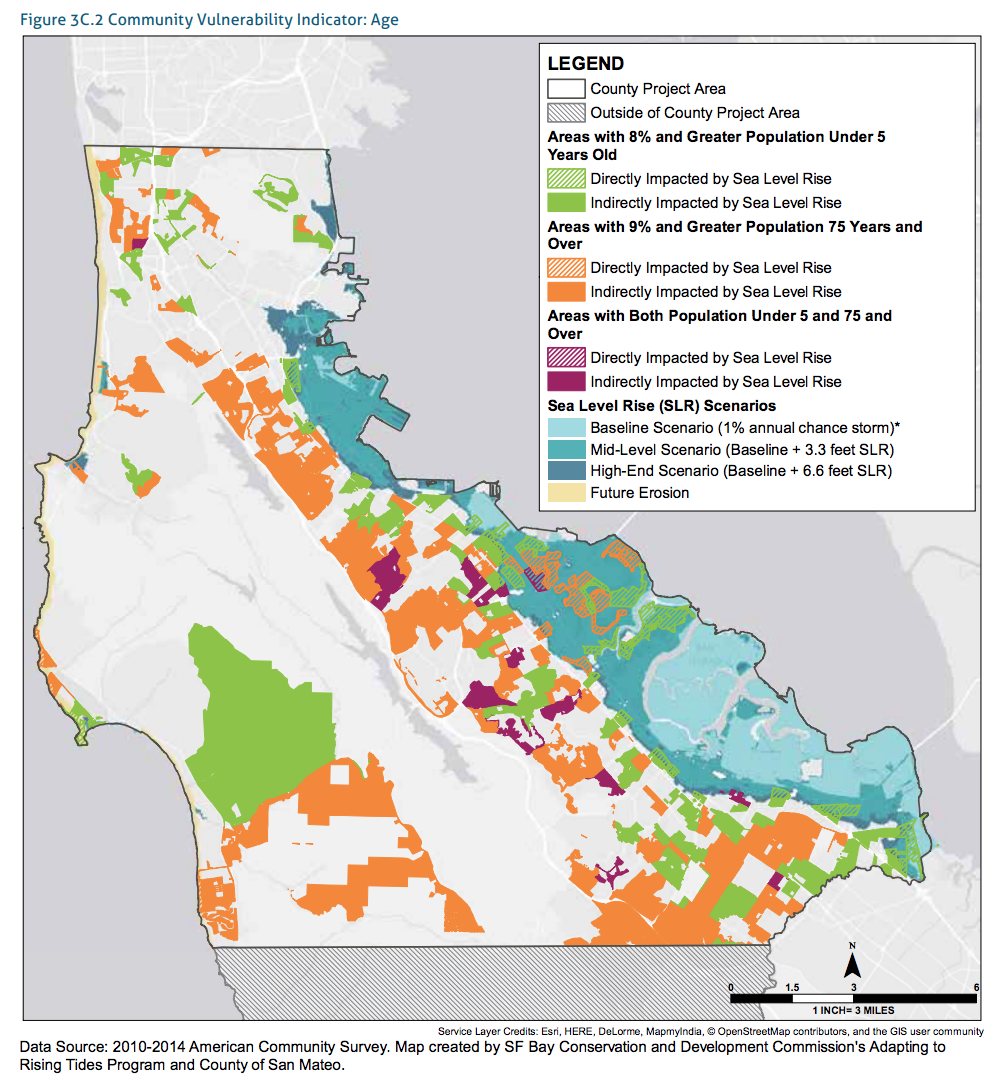
 San Mateo image Community Vulnerability map | |
| Team Organizations | Cybertrust America City of San Mateo |
| Point of Contact | Lan Jenson |
| Participating Municipalities | San Mateo CA |
| Sectors | Cybersecurity and Privacy |
| Initiative | |
| Status | Concept only Stage |
| Last Updated | May 13, 2026 |
Summary
This use case describes how risk assessment has been implemented in the County of San Mateo, California, and identifies activities that align most closely with the Step 0: Prepare and Step 6: Monitor steps of the risk management process. However, the assessment process and the outputs from the assessment also involve elements from and inform all of the other risk management steps (i.e., Step 1: Categorize, Step 2: Select, Step 3: Implement, Step 4: Assess, Step 5: Authorize). Refer to Appendix B of this Guidebook for an example of the risk assessment questionnaire and its application.
The County of San Mateo uses a Risk Assessment Questionnaire to ensure that technology projects are aligned with the County’s Information Security Policy. The Risk Assessment Questionnaire must be completed and then subsequently reviewed and approved by the Chief Information Security Officer’s (CISO’s) Security Analyst before a project is approved by the Program Management Office; hence, it serves as a controlling mechanism for compliance with the Information Security Policy.
The Risk Assessment Questionnaire establishes a control process from the CISO’s office that has expert security review and analysis of key aspects of any projects where cybersecurity and privacy risks need to be reviewed and deemed compliant with the County of San Mateo’s Information Security Policy.
The Security Analyst follows the existing Information Security Policy, which covers requirements such as roles/responsibilities, signed NDAs, HIPAA mandates, and procurement reviews, when reviewing the answers to the questionnaire. Ultimately, the risk assessment process informs the Program Manager and all of the project’s stakeholders on the Information Security Policy compliance requirements. By identifying and substantiating risks associated with specific projects, risk response decisions (e.g., risk mitigation, risk acceptance) can be made.