Connected Vehicle Pilot Security Management Operating Concept
| Connected Vehicle Pilot Security Management Operating Concept | |
 Connected Vehicle Pilot Deployment Program | |
| Team Organizations | Tampa-Hillsborough Expressway Authority (THEA) |
| Point of Contact | Katherine Hartman |
| Participating Municipalities | Tampa FL |
| Sectors | Cybersecurity and Privacy Transportation |
| Initiative | |
| Status | Launched |
| Last Updated | April 29, 2026 |
Summary
Development of a Security Management Operating Concept (SMOC) for phase I of the Tampa Hillsborough Expressway Authority (THEA) Connected Vehicle (CV) Pilot Deployment Program. This focuses on how the THEA team developed an approach to the SMOC (i.e., Prepare); categorized information flows and systems (i.e., Categorize); and selected security controls to establish draft, minimum security control baselines (i.e., Select). The resulting SMOC is largely based on the NIST RMF and provides guidance for ensuring “the privacy of pilot participants and the overall security of the Vehicle-to-Everything (V2X) system for the THEA CV Pilot.”
The THEA CV Pilot Deployment Program is sponsored by the U.S. Department of Transportation’s (DOT) Intelligent Transportation Systems Joint Program Office and is focused on leveraging vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I) technology to improve traffic safety, congestion, and emissions in Tampa, Florida.
Some smart transportation applications that may leverage the V2V and V2I technologies include intelligent signal systems; pedestrian collision warnings; transit signal priority systems; and wrong way entry warnings.
Step 0: Prepare
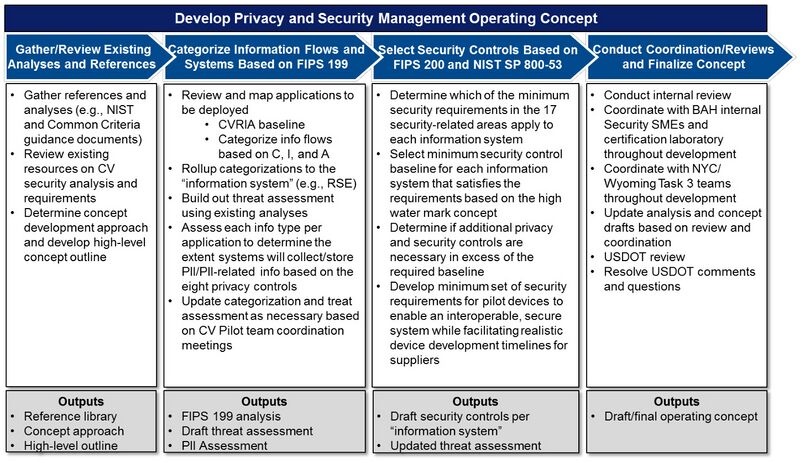
In this initial step, the THEA team conducted three primary activities:
- Gather references (e.g., FIPS 140-2, Common Criteria) and existing analyses (e.g., CAMP V2V-Interoperability reports, European Telecommunications Standards Institute (ETSI) Threat, Vulnerability and Risk Analysis (TVRA))
- Review existing resources on CV security analysis and requirements (e.g., DOT Security Credential Management System)
- Determine SMOC approach and develop high-level SMOC outline
Step 1: Categorize
In the next step, the team identified all information flows for each application in the Pilot and categorized them using Confidentiality, Integrity, and Availability criteria from FIPS 199. Devices that act as either source of destination for information flows were further categorized by the types of information and those Confidentiality, Integrity, and Availability criteria. Lastly, information flows were also assessed against privacy-specific criteria.
The following bullets summarize the primary activities of this step:
- Review and map smart transportation applications to be deployed
- Categorize information flows based on Confidentiality, Integrity, and Availability
Rollup information flow categorizations to the “information system”
- Supplement threat assessment with existing analyses
- Assess each information type for each application to determine extent systems will collect or store PII or PII-related information
- Update categorization and threat assessment, as necessary, based on CV Pilot team meetings
Step 2: Select
Based on the threat assessment and the categorization of information types, devices, and systems, the THEA team selected security controls and created minimum security control baselines for CV Pilot devices and systems. This exercise leveraged the FIPS 200 and NIST SP 800-53 resources and focused on areas such as communications, access, hardware, software, and operating system security considerations.
The primary activities included the following:
- Determine which security controls and requirements apply to each information system
- Select minimum security control baseline for each information system
- Determine if additional security and privacy controls are necessary beyond the baseline
- Develop minimum security requirements for pilot devices that balance interoperability, security, privacy, and realistic device development timelines for suppliers
Development of the THEA Privacy and Security Management Concept
The operating concept was reviewed, revised, and finalized with coordination across and input from multiple teams, including the THEA team, DOT, security experts, and testing labs. The SMOC authors recognize that the concept and the requirements included within it may need to be updated based on new inputs.